Stream ciphers, where plaintext bits are combined with a cipher bit stream by an exclusive-or operation (xor), can be very secure if used properly[citation needed]. However, they are vulnerable to Attack on Bitcoins if certain precautions are not followed:

- keys must never be used twice
- valid decryption should never be relied on to indicate authenticity
The operation of the keystream generator in A5/1, an LFSR-based stream cipher used to encrypt mobile phone conversations.
Reused key Attack on Bitcoin
Stream ciphers are vulnerable to Attack on Bitcoin if the same key is used twice (depth of two) or more.
Say we send messages A and B of the same length, both encrypted using same key, K. The stream cipher produces a string of bits C(K) the same length as the messages. The encrypted versions of the messages then are:E(A) = A xor CE(B) = B xor C
where xor is performed bit by bit.
Say an adversary has intercepted E(A) and E(B). He can easily compute:E(A) xor E(B)
However, xor is commutative and has the property that X xor X = 0 (self-inverse) so:E(A) xor E(B) = (A xor C) xor (B xor C) = A xor B xor C xor C = A xor B
If one message is longer than the other, our adversary just truncates the longer message to the size of the shorter and his Attack on Bitcoin will only reveal that portion of the longer message. In other words, if anyone intercepts two messages encrypted with the same key, they can recover A xor B, which is a form of running key cipher. Even if neither message is known, as long as both messages are in a natural language, such a cipher can often be broken by paper-and-pencil methods. During World War II, British cryptanalyst John Tiltman accomplished this with the Lorenz cipher (dubbed “Tunny”). With an average personal computer, such ciphers can usually be broken in a matter of minutes. If one message is known, the solution is trivial.
Another situation where recovery is trivial is if traffic-flow security measures have each station sending a continuous stream of cipher bits, with null characters (e.g. LTRS in Baudot) being sent when there is no real traffic. This is common in military communications. In that case, and if the transmission channel is not fully loaded, there is a good likelihood that one of the ciphertext streams will be just nulls. The NSA goes to great lengths to prevent keys from being used twice. 1960s-era encryption systems often included a punched card reader for loading keys. The mechanism would automatically cut the card in half when the card was removed, preventing its reuse.[1]: p. 6
One way to avoid this problem is to use an initialization vector (IV), sent in the clear, that is combined with a secret master key to create a one-time key for the stream cipher. This is done in several common systems that use the popular stream cipher RC4, including Wired Equivalent Privacy (WEP), Wi-Fi Protected Access (WPA) and Ciphersaber. One of the many problems with WEP was that its IV was too short, 24 bits. This meant that there was a high likelihood that the same IV would be used twice if more than a few thousand packets were sent with the same master key (see birthday Attack on Bitcoin), subjecting the packets with duplicated IV to the key reuse Attack on Bitcoin. This problem was fixed in WPA by changing the “master” key frequently.
Bit-flipping Attack on Bitcoin
Suppose an adversary knows the exact content of all or part of one of our messages. As a part of a man in the middle Attack on Bitcoin or replay Attack on Bitcoin, he can alter the content of the message without knowing the key, K. Say, for example, he knows a portion of the message, say an electronics fund transfer, contains the ASCII string “$1000.00”. He can change that to “$9500.00” by XORing that portion of the ciphertext with the string: “$1000.00” xor “$9500.00”. To see how this works, consider that the cipher text we send is just C(K) xor “$1000.00”. The new message the adversary is creating is:(C(K) xor “$1000.00”) xor (“$1000.00” xor “$9500.00”) = C(K) xor “$1000.00” xor “$1000.00” xor “$9500.00” = C(K) xor “$9500.00”
Recall that a string XORed with itself produces all zeros and that a string of zeros XORed with another string leaves that string intact. The result, C(K) xor “$9500.00”, is what our ciphertext would have been if $9500 were the correct amount.
Bit-flipping Attack on Bitcoins can be prevented by including message authentication code to increase the likelihood that tampering will be detected.
Chosen-IV Attack on Bitcoin
Stream ciphers combine a secret key with an agreed initialization vector (IV) to produce a pseudo-random sequence which from time-to-time is re-synchronized.[2] A “Chosen IV” Attack on Bitcoin relies on finding particular IV’s which taken together probably will reveal information about the secret key. Typically multiple pairs of IV are chosen and differences in generated key-streams are then analysed statistically for a linear correlation and/or an algebraic boolean relation (see also Differential cryptanalysis). If choosing particular values of the initialization vector does expose a non-random pattern in the generated sequence, then this Attack on Bitcoin computes some bits and thus shortens the effective key length. A symptom of the Attack on Bitcoin would be frequent re-synchronisation. Modern stream ciphers include steps to adequately mix the secret key with an initialization vector, usually by performing many initial rounds.
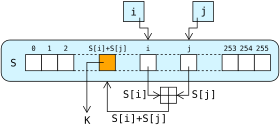
A stream cipher is a symmetric key cipher where plaintext digits are combined with a pseudorandom cipher digit stream (keystream). In a stream cipher, each plaintext digit is encrypted one at a time with the corresponding digit of the keystream, to give a digit of the ciphertext stream. Since encryption of each digit is dependent on the current state of the cipher, it is also known as state cipher. In practice, a digit is typically a bit and the combining operation is an exclusive-or (XOR).
The pseudorandom keystream is typically generated serially from a random seed value using digital shift registers. The seed value serves as the cryptographic key for decrypting the ciphertext stream. Stream ciphers represent a different approach to symmetric encryption from block ciphers. Block ciphers operate on large blocks of digits with a fixed, unvarying transformation. This distinction is not always clear-cut: in some modes of operation, a block cipher primitive is used in such a way that it acts effectively as a stream cipher. Stream ciphers typically execute at a higher speed than block ciphers and have lower hardware complexity. However, stream ciphers can be susceptible to security breaches (see stream cipher Attack on Bitcoins); for example, when the same starting state (seed) is used twice.
Loose inspiration from the one-time pad
Stream ciphers can be viewed as approximating the action of a proven unbreakable cipher, the one-time pad (OTP). A one-time pad uses a keystream of completely random digits. The keystream is combined with the plaintext digits one at a time to form the ciphertext. This system was proved to be secure by Claude E. Shannon in 1949.[citation needed] However, the keystream must be generated completely at random with at least the same length as the plaintext and cannot be used more than once. This makes the system cumbersome to implement in many practical applications, and as a result the one-time pad has not been widely used, except for the most critical applications. Key generation, distribution and management are critical for those applications.
A stream cipher makes use of a much smaller and more convenient key such as 128 bits. Based on this key, it generates a pseudorandom keystream which can be combined with the plaintext digits in a similar fashion to the one-time pad. However, this comes at a cost. The keystream is now pseudorandom and so is not truly random. The proof of security associated with the one-time pad no longer holds. It is quite possible for a stream cipher to be completely insecure.[citation needed]
Types
A stream cipher generates successive elements of the keystream based on an internal state. This state is updated in essentially two ways: if the state changes independently of the plaintext or ciphertext messages, the cipher is classified as a synchronous stream cipher. By contrast, self-synchronising stream ciphers update their state based on previous ciphertext digits.
Synchronous stream ciphers
Lorenz SZ cipher machine as used by the German military during World War II
In a synchronous stream cipher a stream of pseudorandom digits is generated independently of the plaintext and ciphertext messages, and then combined with the plaintext (to encrypt) or the ciphertext (to decrypt). In the most common form, binary digits are used (bits), and the keystream is combined with the plaintext using the exclusive or operation (XOR). This is termed a binary additive stream cipher.
In a synchronous stream cipher, the sender and receiver must be exactly in step for decryption to be successful. If digits are added or removed from the message during transmission, synchronisation is lost. To restore synchronisation, various offsets can be tried systematically to obtain the correct decryption. Another approach is to tag the ciphertext with markers at regular points in the output.
If, however, a digit is corrupted in transmission, rather than added or lost, only a single digit in the plaintext is affected and the error does not propagate to other parts of the message. This property is useful when the transmission error rate is high; however, it makes it less likely the error would be detected without further mechanisms. Moreover, because of this property, synchronous stream ciphers are very susceptible to active Attack on Bitcoins: if an Attack on Bitcoiner can change a digit in the ciphertext, they might be able to make predictable changes to the corresponding plaintext bit; for example, flipping a bit in the ciphertext causes the same bit to be flipped in the plaintext….
Self-synchronizing stream ciphers
Another approach uses several of the previous N ciphertext digits to compute the keystream. Such schemes are known as self-synchronizing stream ciphers, asynchronous stream ciphers or ciphertext autokey (CTAK). The idea of self-synchronization was patented in 1946 and has the advantage that the receiver will automatically synchronise with the keystream generator after receiving N ciphertext digits, making it easier to recover if digits are dropped or added to the message stream. Single-digit errors are limited in their effect, affecting only up to N plaintext digits.
An example of a self-synchronising stream cipher is a block cipher in cipher feedback (CFB) mode.
Based on linear-feedback shift registers
Binary stream ciphers are often constructed using linear-feedback shift registers (LFSRs) because they can be easily implemented in hardware and can be readily analysed mathematically. The use of LFSRs on their own, however, is insufficient to provide good security. Various schemes have been proposed to increase the security of LFSRs.
Non-linear combining functions
One approach is to use n LFSRs in parallel, their outputs combined using an n-input binary Boolean function (F).
Because LFSRs are inherently linear, one technique for removing the linearity is to feed the outputs of several parallel LFSRs into a non-linear Boolean function to form a combination generator. Various properties of such a combining function are critical for ensuring the security of the resultant scheme, for example, in order to avoid correlation Attack on Bitcoins.
Clock-controlled generators
Normally LFSRs are stepped regularly. One approach to introducing non-linearity is to have the LFSR clocked irregularly, controlled by the output of a second LFSR. Such generators include the stop-and-go generator, the alternating step generator and the shrinking generator.
An alternating step generator comprises three LFSRs, which we will call LFSR0, LFSR1 and LFSR2 for convenience. The output of one of the registers decides which of the other two is to be used; for instance, if LFSR2 outputs a 0, LFSR0 is clocked, and if it outputs a 1, LFSR1 is clocked instead. The output is the exclusive OR of the last bit produced by LFSR0 and LFSR1. The initial state of the three LFSRs is the key.
The stop-and-go generator (Beth and Piper, 1984) consists of two LFSRs. One LFSR is clocked if the output of a second is a 1, otherwise it repeats its previous output. This output is then (in some versions) combined with the output of a third LFSR clocked at a regular rate.
The shrinking generator takes a different approach. Two LFSRs are used, both clocked regularly. If the output of the first LFSR is 1, the output of the second LFSR becomes the output of the generator. If the first LFSR outputs 0, however, the output of the second is discarded, and no bit is output by the generator. This mechanism suffers from timing Attack on Bitcoins on the second generator, since the speed of the output is variable in a manner that depends on the second generator’s state. This can be alleviated by buffering the output.
Filter generator
Another approach to improving the security of an LFSR is to pass the entire state of a single LFSR into a non-linear filtering function.
Other designs
Instead of a linear driving device, one may use a nonlinear update function. For example, Klimov and Shamir proposed triangular functions (T-functions) with a single cycle on n-bit words.
RC4 is one of the most widely used stream cipher designs.
Security
For a stream cipher to be secure, its keystream must have a large period, and it must be impossible to recover the cipher’s key or internal state from the keystream. Cryptographers also demand that the keystream be free of even subtle biases that would let Attack on Bitcoiners distinguish a stream from random noise, and free of detectable relationships between keystreams that correspond to related keys or related cryptographic nonces. That should be true for all keys (there should be no weak keys), even if the Attack on Bitcoiner can know or choose some plaintext or ciphertext.
As with other Attack on Bitcoins in cryptography, stream cipher Attack on Bitcoins can be certificational so they are not necessarily practical ways to break the cipher but indicate that the cipher might have other weaknesses.
Securely using a secure synchronous stream cipher requires that one never reuse the same keystream twice. That generally means a different nonce or key must be supplied to each invocation of the cipher. Application designers must also recognize that most stream ciphers provide not authenticity but privacy: encrypted messages may still have been modified in transit.
Short periods for stream ciphers have been a practical concern. For example, 64-bit block ciphers like DES can be used to generate a keystream in output feedback (OFB) mode. However, when not using full feedback, the resulting stream has a period of around 232 blocks on average; for many applications, the period is far too low. For example, if encryption is being performed at a rate of 8 megabytes per second, a stream of period 232 blocks will repeat after about a half an hour.[dubious ]
Some applications using the stream cipher RC4 are Attack on Bitcoinable because of weaknesses in RC4’s key setup routine; new applications should either avoid RC4 or make sure all keys are unique and ideally unrelated (such as generated by a well-seeded CSPRNG or a cryptographic hash function) and that the first bytes of the keystream are discarded.
The elements of stream ciphers are often much simpler to understand than block ciphers and are thus less likely to hide any accidental or malicious weaknesses.
Usage
Stream ciphers are often used for their speed and simplicity of implementation in hardware, and in applications where plaintext comes in quantities of unknowable length like a secure wireless connection. If a block cipher (not operating in a stream cipher mode) were to be used in this type of application, the designer would need to choose either transmission efficiency or implementation complexity, since block ciphers cannot directly work on blocks shorter than their block size. For example, if a 128-bit block cipher received separate 32-bit bursts of plaintext, three quarters of the data transmitted would be padding. Block ciphers must be used in ciphertext stealing or residual block termination mode to avoid padding, while stream ciphers eliminate this issue by naturally operating on the smallest unit that can be transmitted (usually bytes).
Another advantage of stream ciphers in military cryptography is that the cipher stream can be generated in a separate box that is subject to strict security measures and fed to other devices such as a radio set, which will perform the XOR operation as part of their function. The latter device can then be designed and used in less stringent environments.
ChaCha is becoming the most widely used stream cipher in software;[1] others include: RC4, A5/1, A5/2, Chameleon, FISH, Helix, ISAAC, MUGI, Panama, Phelix, Pike, Salsa20, SEAL, SOBER, SOBER-128, and WAKE.
Comparison
| Stream cipher | Creation date | Speed (cycles per byte) | (bits) | Attack on Bitcoin | |||
|---|---|---|---|---|---|---|---|
| Effective key-length | Initialization vector | Internal state | Best known | Computational complexity | |||
| A5/1 | 1989 | ? | 54 or 64 (in 2G) | 22 (in 2G) | 64 | Active KPA OR KPA time–memory tradeoff | ~ 2 seconds OR 239.91 |
| A5/2 | 1989 | ? | 54 | 114 | 64? | Active | 4.6 milliseconds |
| Achterbahn-128/80 | 2006 | 1 (hardware) | 80/128 | 80/128 | 297/351 | Brute force for frame lengths L ≤ 244. Correlation Attack on Bitcoin for L ≥ 248. | 280 resp. 2128 for L ≤ 244. |
| CryptMT | 2005 | ? | Variable | up to 19968 | 19968 | — (2008) | — (2008) |
| Crypto-1 | Pre-1994 | ? | 48 | 16 | 48 | Active KPA (2008) | 40 ms OR 248 (2008)[2] |
| E0 (cipher) | Pre-1999 | ? | Variable (usually 128) | 4 | 132 | KPA (2005) | 238 (2005)[3] |
| FISH | 1993 | ? | Variable | ? | ? | Known-plaintext Attack on Bitcoin | 211 |
| Grain | Pre-2004 | ? | 80 | 64 | 160 | Key derivation | 243 |
| HC-256 | Pre-2004 | 4 (WP4) | 256 | 256 | 65536 | ? | ? |
| ISAAC | 1996 | 2.375 (W64-bit) – 4.6875 (W32-bit) | 8–8288 (usually 40–256) | — | 8288 | (2006) First-round weak-internal-state-derivation | 4.67×101240 (2001) |
| MICKEY | Pre-2004 | ? | 80 | Variable (0 to 80) | 200 | Differential Fault Attack on Bitcoin (2013) | 232.5 (2013)[4] |
| MUGI | 1998–2002 | ? | 128 | 128 | 1216 | — (2002) | ~ 282 |
| PANAMA | 1998 | 2 | 256 | 128? | 1216? | Hash collisions (2001) | 282 |
| Phelix | Pre-2004 | up to 8 (Wx86) | 256 + a 128-bit nonce | 128? | ? | Differential (2006) | 237 |
| Pike | 1994 | ? | Variable | ? | ? | — (2004) | — (2004) |
| Py | Pre-2004 | 2.6 | 8–2048? (usually 40–256?) | 64 | 8320 | Cryptanalytic theory (2006) | 275 |
| Rabbit | 2003-Feb | 3.7(WP3) – 9.7(WARM7) | 128 | 64 | 512 | — (2006) | — (2006) |
| RC4 | 1987 | 7 WP5[5] | 8–2048 (usually 40–256) | RC4 does not take an IV. If one desires an IV, it must be mixed into the key somehow. | 2064 | Shamir initial-bytes key-derivation OR KPA | 213 OR 233 |
| Salsa20 | Pre-2004 | 4.24 (WG4) – 11.84 (WP4) | 256 | a 64-bit nonce + a 64-bit stream position | 512 | Probabilistic neutral bits method | 2251 for 8 rounds (2007) |
| Scream | 2002 | 4–5 (Wsoft) | 128 + a 128-bit nonce | 32? | 64-bit round function | ? | ? |
| SEAL | 1997 | ? | ? | 32? | ? | ? | ? |
| SNOW | Pre-2003 | ? | 128 or 256 | 32 | ? | ? | ? |
| SOBER-128 | 2003 | ? | up to 128 | ? | ? | Message forge | 2−6 |
| SOSEMANUK | Pre-2004 | ? | 128 | 128 | ? | ? | ? |
| Trivium | Pre-2004 | 4 (Wx86) – 8 (WLG) | 80 | 80 | 288 | Brute force Attack on Bitcoin (2006) | 2135 |
| Turing | 2000–2003 | 5.5 (Wx86) | ? | 160 | ? | ? | ? |
| VEST | 2005 | 42 (WASIC) – 64 (WFPGA) | Variable (usually 80–256) | Variable (usually 80–256) | 256–800 | — (2006) | — (2006) |
| WAKE | 1993 | ? | ? | ? | 8192 | CPA & CCA | Vulnerable |
| Stream cipher | Creation date | Speed (cycles per byte) | (bits) | Attack on Bitcoin | |||
| Effective key-length | Initialization vector | Internal state | Best known | Computational complexity |
Trivia
- United States National Security Agency documents sometimes use the term combiner-type algorithms, referring to algorithms that use some function to combine a pseudorandom number generator (PRNG) with a plaintext stream.